Security researchers are warning that Vidar Stealer infections are likely to increase after the malware developer released a new major version with upgraded capabilities.
According to an announcement from the developer this month, Vidar 2.0 has been rewritten in C, supports multi-threading data stealing, bypasses Chrome’s app-bound encryption, and features more advanced evasion mechanisms.
Infostealer malware specializesin stealing data frombrowsers and other apps, including passwords, credit card information, and cryptocurrency wallet information.
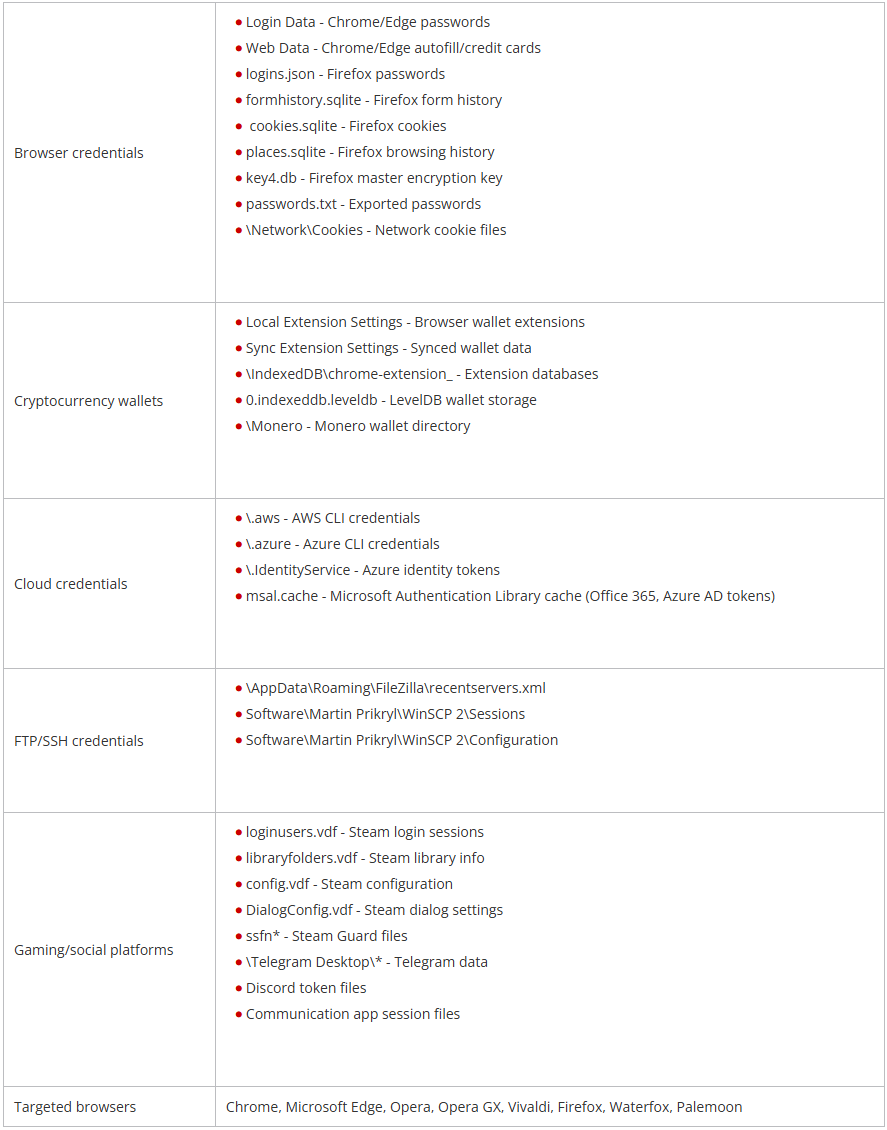 report fromTrend Micro researchers, Vidar activity has spiked since the release of its second major version, which comes with the following highlights:
report fromTrend Micro researchers, Vidar activity has spiked since the release of its second major version, which comes with the following highlights:
- Complete rewrite from C++ to C, now relying on fewer dependencies and having better raw performance at a much smaller footprint.
- Multi-thread CPU support where data-stealing worker threads are spawned simultaneously to parallelize collection and reduce dwell time.
- Extensive anti-analysis checks, including debugger detection, timing checks, uptime, and hardware profiling.
- Builder offers polymorphism options with heavy control-flow flattening and numeric state-machine switch constructs, making static detection more difficult.
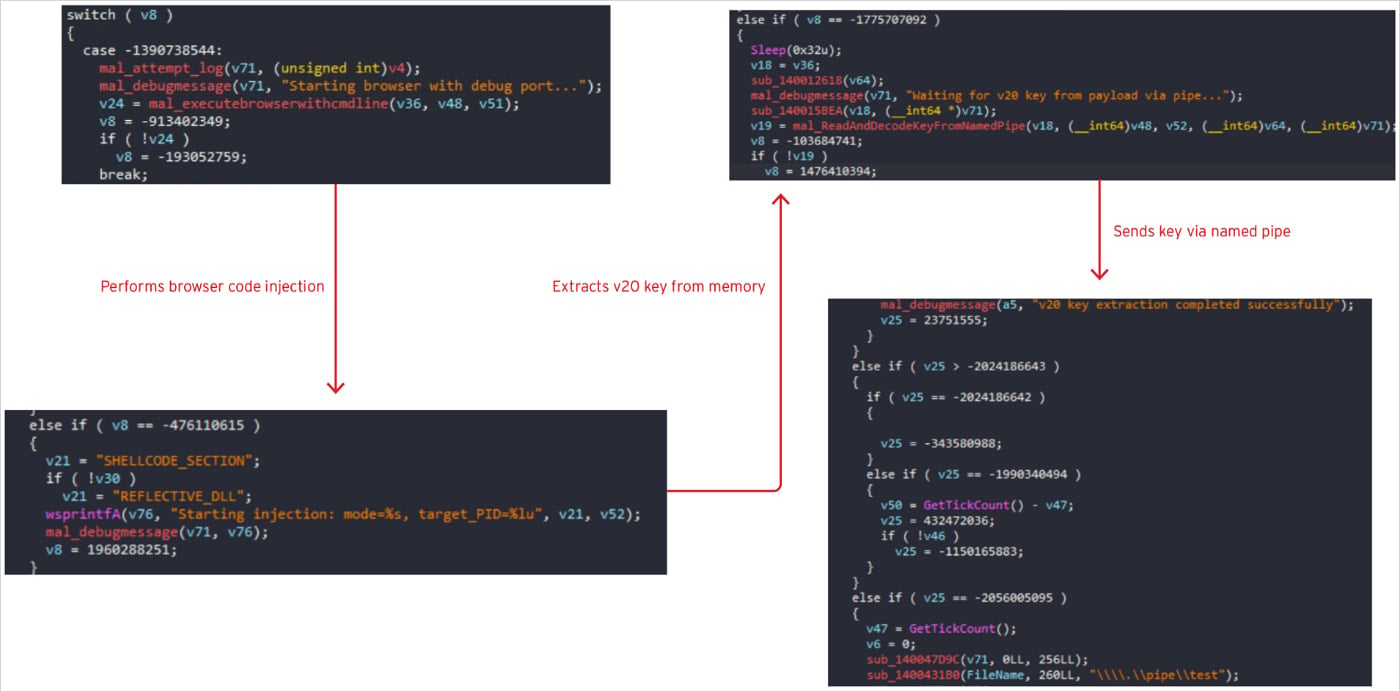
- Evasion of Chrome’s App-Bound encryption protection by means of memory injection techniques.
“The malware also employs an advanced technique that launches browsers with debugging enabled and injects malicious code directly into running browser processes using either shellcode or reflective DLL injection,” explains Trend Micro.
“The injected payload extracts encryption keys directly from browser memory, then communicates the stolen keys back to the main malware process via named pipes to avoid disk artifacts.”
“This approach can bypass Chrome’s AppBound encryption protections by stealing keys from active memory rather than attempting to decrypt them from storage.”
 introduced in July 2024, has been bypassed by multiple info-stealer malware families over time.
introduced in July 2024, has been bypassed by multiple info-stealer malware families over time.
Once Vidar 2.0 collectsall the data it can access on the infected machine, it captures screenshots, packages everything, and sends it to delivery points that includeTelegram bots and URLs stored on Steam profiles.
Trend Micro researchers expect Vidar 2.0 to become more prevalent in campaigns through Q4 2025 as the “malware’s technical capabilities, proven developer track record since 2018, and competitive pricing position it as a likely successor to Lumma Stealer’s dominant market position.”
Bill Toulas
Bill Toulas is a tech writer and infosec news reporter with over a decade of experience working on various online publications, covering open-source, Linux, malware, data breach incidents, and hacks.