Russian Lynk group leaks sensitive UK MoD files, including info on eight military bases
Russian hackers stole and leaked MoD files on eight RAF and Navy bases, exposing staff data in a “catastrophic” cyberattack via Dodd Group breach.
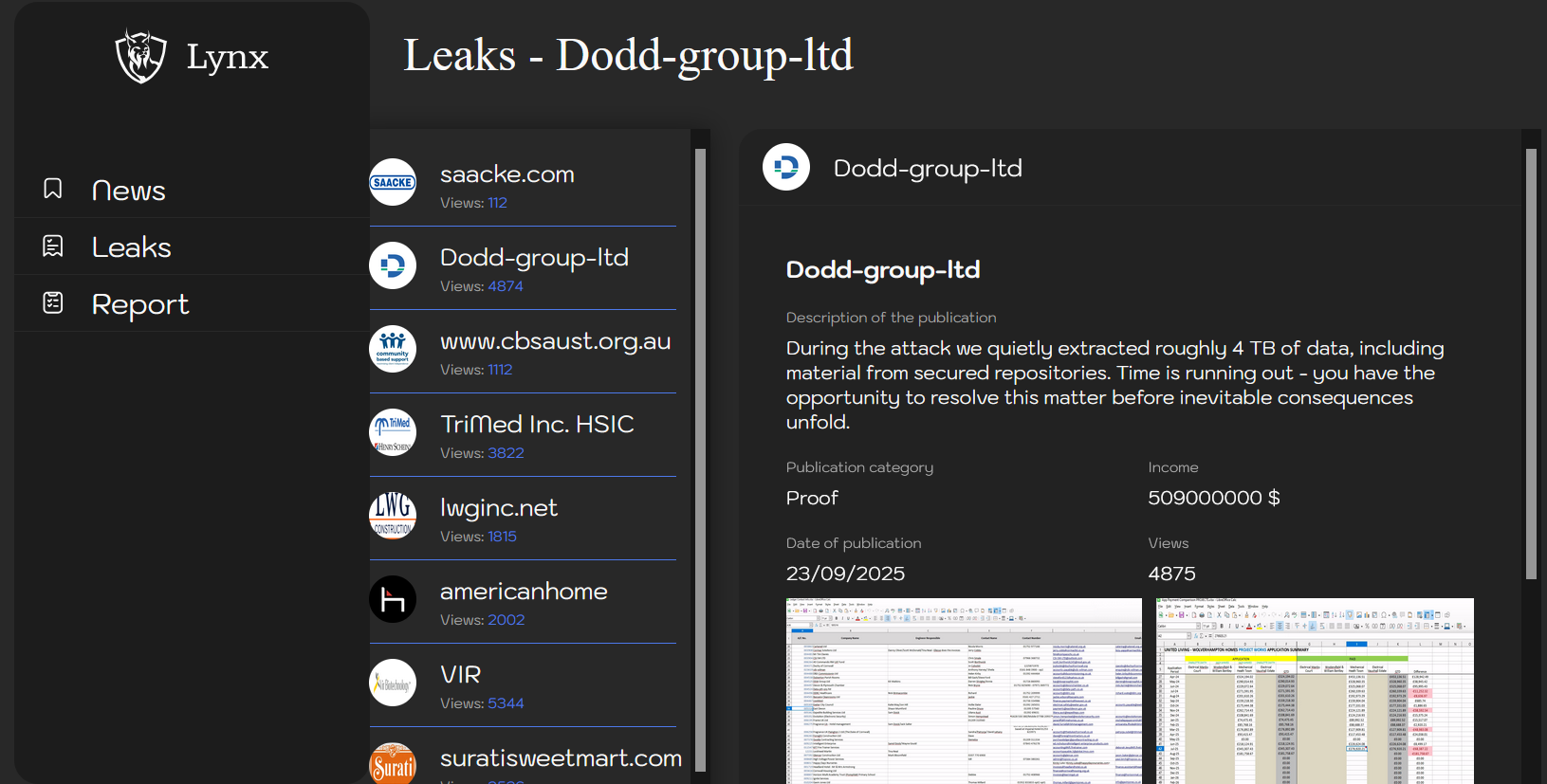
Russian cybercrime group Lynx breached Dodd Group, a contractor for the UK Ministry of Defence, stealing and leaking hundreds of sensitive files on eight RAF and Royal Navy bases. The incident occurred on 23 September, The Daily Mail labeled the attack as “catastrophic.”
Compromised data includes staff names and emails, contractors’ names, phone numbers, car details, and MoD staff contacts, with some documents labeled “Controlled” or “Official Sensitive.”
Dodd Group employs over 1,100 people, the company delivers major projects across education, healthcare, housing, utilities, and defence sectors, including maintenance and construction work for the UK Ministry of Defence. It remains one of Britain’s leading privately owned engineering and facilities management firms.
The ransomware gang added the company to its Tor data leak site claiming the theft of roughly 4 TB of data. The group already started leaking the stolen data, likely after a failed negotiation.
Leaked MoD documents reveal sensitive details on RAF and Navy bases, including Lakenheath (hosting US F-35 jets), Portreath (NATO radar site), and Predannack (UK Drone Hub), as per the The Daily Mail.
“Leaked documents seen by the MoS disclose information about a number of sensitive RAF and Navy bases, including RAF Lakenheath, in Suffolk, where the US Air Force’s F-35 stealth jets are based and theirnuclear bombsare believed to be housed.” reported The Daily Mail.
“Other bases include RAF Portreath – a top-secret radar station that forms part ofNato’s air defence network – and RAF Predannack, now home to the UK’s National Drone Hub.”
Leaked files include around 1,000 documents: visitor logs for RAF Portreath and RNAS Culdrose, internal emails and security guidance, plus construction records for RAF Lakenheath and RAF Mildenhall, revealing sensitive operational details.
The Dodd Group disclosed the data breach, a company spokesman said that only ‘limited data’ had been stolen.
Intelligence experts warn that nation-state actors can use the stolen data for intelligence purposes or to carry out further cyber attacks against the impacted organizations.
The MoD launched an investigation into the incident.
Follow me on Twitter:@securityaffairsandFacebookandMastodon
(SecurityAffairs–hacking,UK MoD )