Bangladesh cyber security watchdog BGD e-GOV CIRT published an advisory (27.10.2025) regarding critical romote code execution vulnarability in Microsoft WSUS CVSS score 9.8 as per NVD, NIST.
CIRT has detected a serious security flaw in Microsoft’s WSUS that could let an attacker fully control a WSUS server. This vulnerability not only impacts the server but could also enable the attacker to send harmful updates, compromise devices, and gain significant access to our network. It considers this a high-priority incident and urge immediate patching or mitigation for all WSUS servers. Inaction could result in regulatory, operational, and reputational harm.
Vulnerability Summary:
The critical remote code execution (RCE) vulnerability has been identified in Microsoft WSUS. The flaw stems from deserialization of untrusted data in WSUS reporting web services and allows an unauthenticated attacker to send specially crafted requests to a WSUS server (with the WSUS Server Role enabled) and execute arbitrary code as NT AUTHORITYSYSTEM. The issue has been assigned a CVSS 3.x score of 9.8 (per NVD/NIST) and is listed in CISA’s Known Exploited Vulnerabilities catalog.
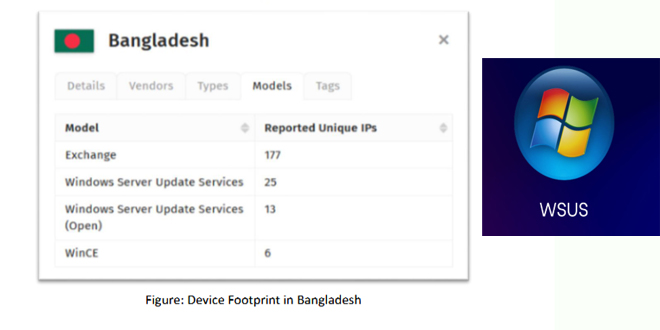
Affected Systems & Scope:
Only Windows servers with the WSUS role enabled are affected. Servers without WSUS aren’t vulnerable. Commonly exposed ports for WSUS are TCP 8530 (HTTP) and TCP 8531 (HTTPS); servers on these ports may be at higher risk.
All Windows Server versions with WSUS enabled are vulnerable unless patched. Vendors provide specific KBs for each OS version. Although WSUS usually operates internally, the risk remains high if a WSUS server is accessible.
Impact:
• Successful exploitation grants the attacker remote code execution with SYSTEM privileges on the WSUS server. This means full compromise of that server.
If compromised, the attacker could use the WSUS server to move laterally, distribute harmful updates, gain higher privileges, or deploy additional payloads.
As WSUS is a patch-distribution infrastructure, compromise may undermine trust in the update process or allow poisoning of updates.
IOCs:
Recomendations:
The Cyber Incident Response Team (CIRT) has advised immediate actions to address the critical WSUS vulnerability. Within 24–72 hours, inventory all WSUS servers to assess their exposure, checking if they are accessible internally or externally and if TCP ports 8530 and 8531 are open. Administrators should install the out-of-band security update from Microsoft dated 23 October 2025 and reboot the servers to apply it. If patching cannot be done right away, temporarily disable the WSUS Server Role or block traffic to ports 8530 and 8531 at the host and network firewall to avoid exploitation.