APT InedibleOchotense, vinculado à Rússia, personifica a ESET para implantar backdoor em sistemas ucranianos
O grupo InedibleOchotense, ligado à Rússia, usou instaladores falsos da ESET em ataques de phishing contra alvos ucranianos em maio de 2025.
O grupo InedibleOchotense, ligado à Rússia, usou instaladores ESET trojanizados em ataques de phishing contra entidades ucranianas detectados em maio de 2025. A campanha usou e-mails e mensagens do Signal para entregar instaladores ESET trojanizados que instalaram software legítimo e o Backdoor Kalambur.
“Outro agente de ameaças alinhado à Rússia, InedibleOchotense, conduziu uma campanha de spearphishing se passando pela ESET. Esta campanha envolveu e-mails e mensagens do Signal entregando um instalador ESET trojanizado que leva ao download de um produto ESET legítimo junto com o backdoor Kalampur.” lê o relatório publicado pela ESET.
O grupo alinhado à Rússia enviou e-mails de phishing e mensagens do Signal contendo links para instaladores ESET trojanizados hospedados em domínios falsos. A campanha compartilha táticas com atividades anteriormente atribuídas ao UAC-0212 e ao downloader BACKORDER.
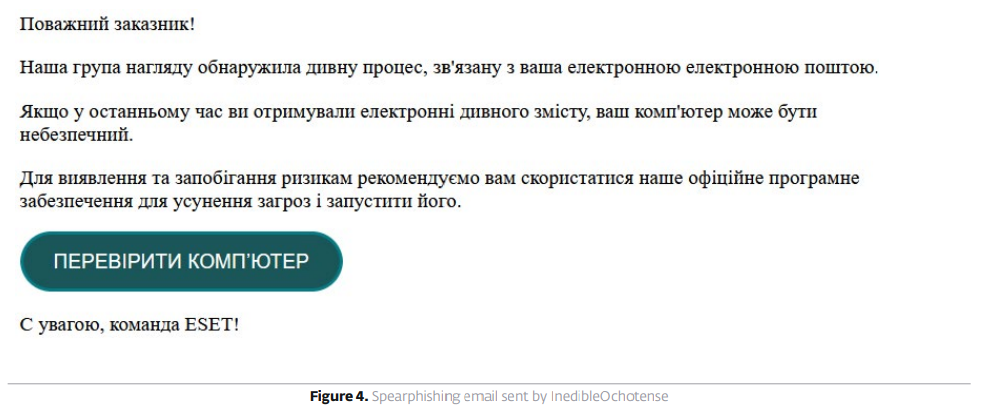
Os pesquisadores notaram que as mensagens continham pequenos erros de linguagem, sugerindo uma tradução ruim do russo para o ucraniano.
O e-mail de phishing se passando pela ESET alertou os usuários sobre atividades suspeitas vinculadas ao seu e-mail e pediu que baixassem o “software oficial de remoção de ameaças”. O link direcionava as vítimas para domínios ESET falsos (por exemplo, esetsmart[.]com, esetscanner[.]com, esetremover[.]com) hospedando um arquivo ZIP com um ESET AV Remover legítimo e um backdoor Kalampur.
O grupo InedibleOchotense explorou a forte reputação da ESET na Ucrânia para induzir os usuários a instalar malware.
Siga-me no Twitter:@securityaffairseLinkedineMastodonte
(Assuntos de Segurança–hacking,boletim informativo)