Safepay ransomware group claims the hack of professional video surveillance provider Xortec
Safepay group claims the hack of professional video surveillance provider Xortec and added the company to its data leak site.
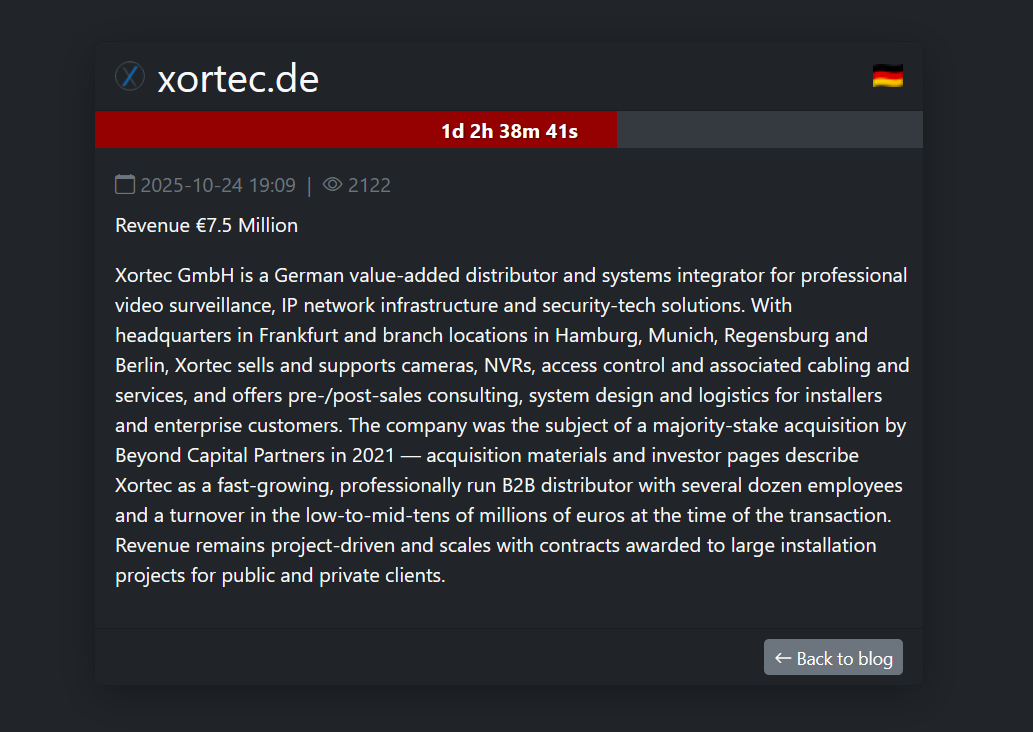
The Safepay group claimed responsibility for hacking German video surveillance provider Xortec and listed the company on its data leak site. The ransomware payment deadline is October 27, 2025.
Xortec GmbH, based in Frankfurt with offices across Germany, is a value-added distributor and systems integrator specializing in video surveillance, IP networking, and security solutions. It provides cameras, NVRs, access control, cabling, and consulting for enterprise and installer clients. Acquired by Beyond Capital Partners in 2021, Xortec is a fast-growing B2B firm with several dozen employees and an annual revenue of over €7.5 million, driven by large installation projects.
Their customers are primarily B2B: system integrators, specialist installers, system houses, and resellers operating globally, especially in the DACH region (Germany, Austria, Switzerland) and broader international markets. Xortec’s offerings underpin security infrastructure for various sectors, including retail, logistics, public and private infrastructure, and critical facilities, given their core focus on video surveillance and communications solutions.
The hack of a company like Xortec could have wide-reaching effects due to its role in the security supply chain. Attackers could backdoor hardware or software used by installers, exposing client data, surveillance layouts, and shipment records. Compromised firmware could undermine trust in thousands of deployed systems. Disruption of Xortec’s logistics could affect resellers and end users, including critical sectors like transport or utilities—making the breach a systemic, multi-tier risk beyond a single company.
A hack of Xortec could have wide-reaching effects due to its role in the security supply chain. Attackers could backdoor hardware or software used by installers, exposing client data, surveillance layouts, and shipment records. Hacked or altered firmware could damage trust in thousands of security systems already in use. If Xortec’s logistics are disrupted, it could impact resellers, customers, and even critical sectors like transport or utilities, turning the breach into a widespread problem that affects far more than just one company.
SafePay is a fast-growing ransomware group that has been active since late 2024. It runs independently, using double extortion, stealing and encrypting data. The group targets global sectors like manufacturing, healthcare, and government. The cybercrime group operates rapidly within 24 hours of access, and avoids Russian systems, suggesting a possible Eastern-European origin.
Follow me on Twitter:@securityaffairsandFacebookandMastodon
(SecurityAffairs–hacking,Safepay ransomware)