A spearphishing attack that lasted a single day targeted members of the Ukrainian regional government administration and organizations critical for the war relief effortin Ukraine, including the International Committee of the Red Cross, UNICEF, and various NGOs.
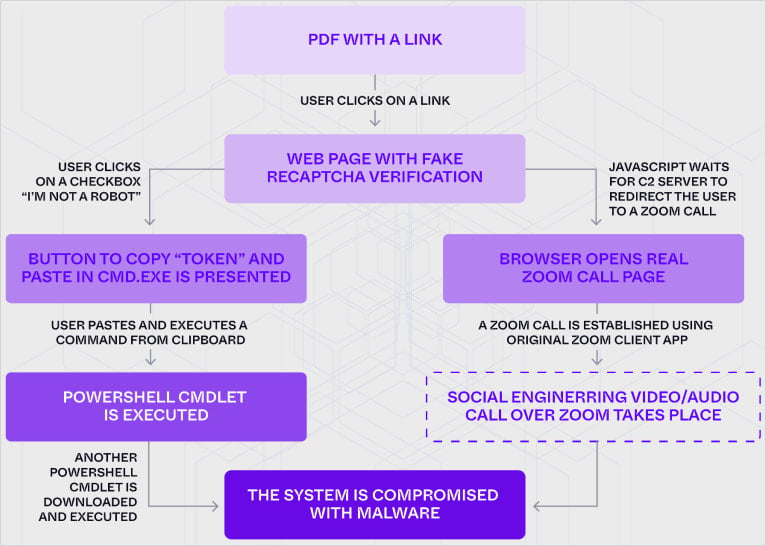
Dubbed PhantomCaptcha, the one-day campaign attempted to trick victims into running commands used in ClickFix attacks, disguised as Cloudflare CAPTCHA verification prompts, to install a WebSocket Remote Access Trojan (RAT).
SentinelLABS, the threat research division at SentinelOne, says that the campaign started and ended on October 8, and that the attacker spent significant time and effort to set up the necessary infrastructure, as some domains used in the operation were registered at the end of March.
“I am not a robot” ClickFix attacks
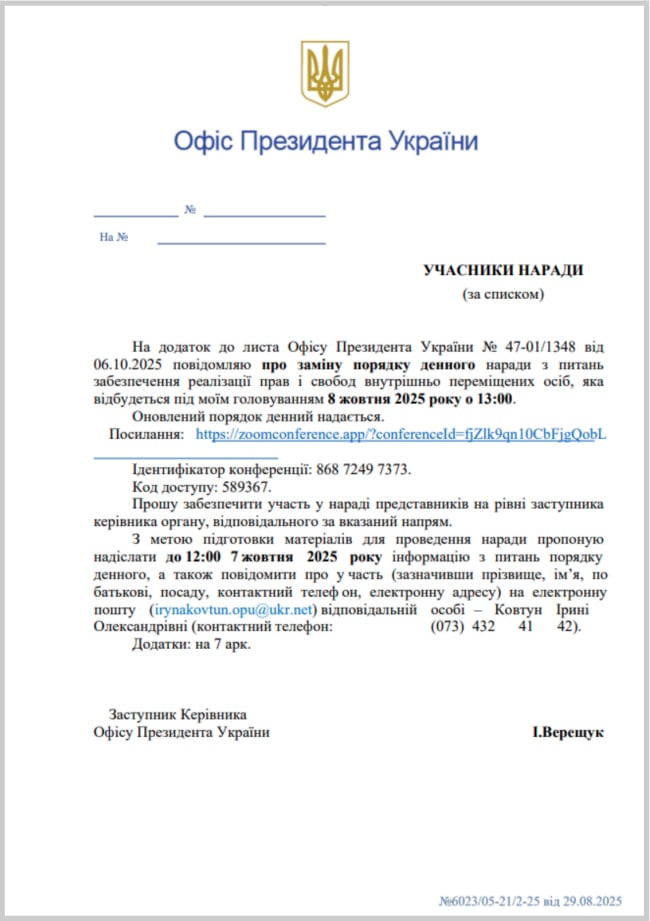
The attacks started with emails impersonating the Ukrainian President’s Office, carrying malicious PDF attachments that linked to a domain impersonating the Zoom (zoomconference[.]app) communication platform.
 SentinelLABS’ analysis showed.
SentinelLABS’ analysis showed.
According to the researchers,this path likely led to the threat actor engaging in live social engineering calls with the victim.
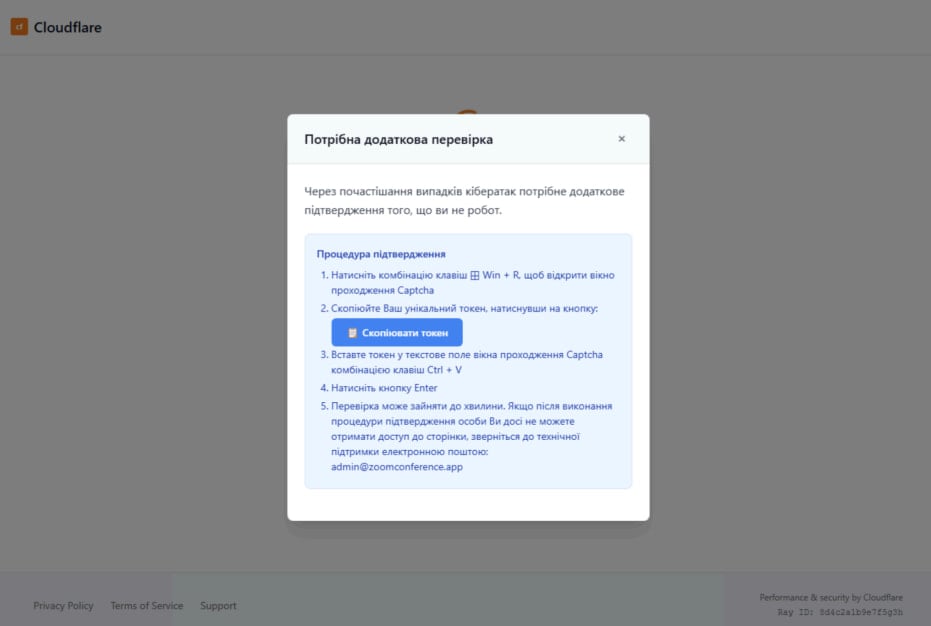
If the client ID did not match, visitors had to pass another security check and prove that they were real people and not robots.
They could complete the fake CAPTCHA verification by following instructions in Ukrainian that prompted them to press a button to copy a “token” and paste itin the WindowsCommand Prompt.
.jpg)
Additionally, a report from the Google Threat Intelligence Group (GTIG) yesterday describes a malicious“I am not a robot” captcha challengeused in attacks attributed to ColdRiver (a.k.a. Star Blizzard, UNC4057, Callisto), a threat group attributed to the Russian intelligence service (FSB).
GTIG highlighted that the hackers were quick to operationalize new malware families after researchers had disclosed publicly older tools that ColdRiver deployed incyberespionage activities.
Bill Toulas
Bill Toulas is a tech writer and infosec news reporter with over a decade of experience working on various online publications, covering open-source, Linux, malware, data breach incidents, and hacks.